Rapid7 recently released our 2024 Attack Intelligence Report, a 14-month deep dive into the vulnerability and attacker landscape. The spiritual successor to our annual Vulnerability Intelligence Report, the AIR includes data from the Rapid7 research team combined with our detection and response and threat intelligence teams. It is designed to provide the clearest view yet into what security professionals face day to day.
In this blog, we would like to focus on one area of research the AIR highlights: network edge technologies. In 2023 (and early 2024) Rapid7 found some startling information about the vulnerability of these critical devices. Essentially, of the mass compromise events we studied, exploitation of network edge tech increased significantly over the 14 months the report covers — something we will cover in detail shortly.
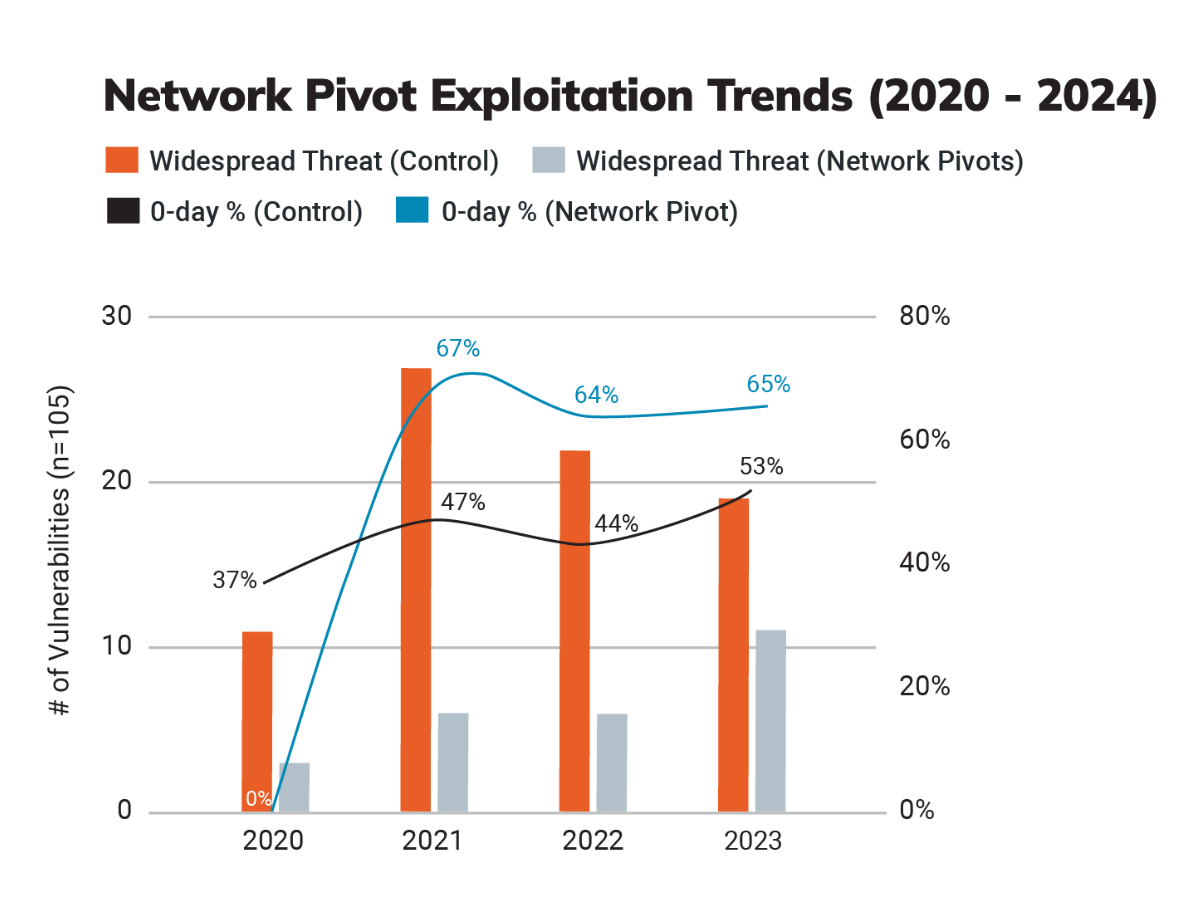
But first, some background. Way back in 2020, Rapid7 created a new attacker utility category for vulnerabilities that functioned as network pivots. These are vulnerabilities that give external attackers internal network access. Think VPNs, firewalls, security gateways, etc. They serve an important function in any network but visibility into these devices can be challenging, making them prime targets for attackers.
In 2023 we saw a surge in attacks on these network appliances. Mass compromise events stemming from exploitation of network edge tech nearly doubled over the period studied — with 36% of all widely exploited vulnerabilities occurring within network perimeter technology. Looking back over the previous reports, we determined some 60% of all of the vulnerabilities Rapid7 analyzed in network edge devices over a three year period were exploited as zero-days, a disproportionate number when looking at the entirety of the vulnerabilities studied.
Over the four years Rapid7 has been categorizing this type of vulnerability, network edge devices have comprised 24% of exploited vulnerabilities and a quarter of all widespread threats.
State-sponsored groups and ransomware groups like Cl0p, Inc, Bl00dy, Akira, Play, LockBit, and more went after network edge tech in 2023. Network edge devices are essential for modern network operations, but they also represent a major weak spot in cybersecurity defenses — one that these organized groups took advantage of in 2023.
There are a number of reasons for this. It can be difficult to detect intrusions on these types of devices as the capabilities for logging and threat detection vary depending on the specific devices used. Some do not log key events, they use a variety of firmware and (often proprietary) operating systems, and in some cases the firmware itself may be encrypted or obfuscated. This makes monitoring and detecting intrusions troublesome across different devices and developing a strategy for the entire spectrum of devices complex.
For more information about network edge technology vulnerabilities, as well as the latest data on ransomware, attacker utilities, widespread threats, file transfer vulns, and more, download the 2024 Attack Intelligence Report.
