Microsoft is addressing 79 vulnerabilities this September 2024 Patch Tuesday. Microsoft has evidence of in-the-wild exploitation and/or public disclosure for four of the vulnerabilities published today; at time of writing, all four are listed on CISA KEV. Microsoft is also patching four critical remote code execution (RCE) vulnerabilities today. Unusually, Microsoft has not patched any browser vulnerabilities yet this month.
Servicing Stack: Windows 10 1507 rollback zero-day RCE
At first glance, the most concerning of today’s exploited-in-the-wild vulnerabilities is CVE-2024-43491, which describes a pre-auth RCE vulnerability caused by a regression in the Windows Servicing Stack that has rolled back fixes for a number of previous vulnerabilities affecting optional components.
The CVSSv3.1 base score is 9.8, which is typically not good news. However, things aren’t quite as bad as they seem: the key takeaway here is that only Windows 10, version 1507 (Windows 10 Enterprise 2015 LTSB and Windows 10 IoT Enterprise 2015 LTSB) is affected. Also, Microsoft notes that while at least some of the accidentally unpatched vulnerabilities were known to be exploited, they haven’t seen in-the-wild exploitation of CVE-2024-43491 itself, and the defect was discovered by Microsoft. All in all, while there are certainly more than a few organizations out there still running Windows 10 1507, most admins can breathe a sigh of relief on this one, and then go back to worrying about everything else.
The Servicing Stack regression described by CVE-2024-43491 was introduced in the March 2024 patches. Those nostalgic few still running Windows 10 1507 should note that patches are required for both Servicing Stack and the regular Windows OS patch released today, and must be applied in that order. Microsoft does not specify which vulnerabilities were accidentally unpatched back in March, although there is a significant list of affected optional components at the end of the FAQ, so potentially the set of vulnerabilities in play is quite long. Given time, an enthusiastic data miner could no doubt come up with a list of likely suspects.
Microsoft does also provide a high-level explanation of what went wrong: the build number of the March 2024 security patch for 1507 triggered a latent code defect in the Servicing Stack, and any optional component which was updated during this time was downgraded to the RTM version. This might sound eerily similar to the Windows OS downgrade attacks disclosed at Black Hat USA 2024 last month, but there’s not obviously any substantial connection between the two. It’s quite likely that someone at Microsoft HQ is carefully reviewing other Windows versions for similar version range-based flaws in the Servicing Stack.
Mark-of-the-Web: zero-day "LNK stomping" security feature bypass
The Mark-of-the-Web (MotW) security feature bypass CVE-2024-38217 is not only known to be exploited, but is also publicly disclosed via an extensive write-up which names the technique "LNK stomping" and highlights that exploitation will typically involve explorer.exe overwriting an existing LNK file. The write-up also links to exploit code on GitHub. Beyond that, the discoverer points to VirusTotal samples going back as far as 2018 to make the case that this has been abused for a very long time indeed.
As is generally the case with MotW bypass vulnerabilities, exploitation occurs when a user downloads and opens a specially-crafted malicious file, which could then bypass the SmartScreen Application Reputation security check and/or the legacy Windows Attachment Services security prompt.
Windows Installer: zero-day EoP
Next up in today’s foursome of exploited-in-the-wild vulnerabilities is CVE-2024-38014: an elevation of privilege vulnerability in Windows Installer. The middling CVSSv3.1 base score of 7.8 lines up with Microsoft’s severity assessment of Important rather than Critical. Exploitation grants code execution as SYSTEM, and although the attack vector is local, this might be at least slightly attractive to malware authors, since both attack complexity and privilege requirements are low, and no user interaction is required.
In this case, CWE-269: Improper Privilege Management presumably describes a means of causing the Windows Installer to be over-generous with the privileged access it requires to install software and configure the OS. All current versions of Windows receive a fix, as well as Server 2008, which Microsoft persists in patching from time to time out of the goodness of its heart, even if the end of official support was almost a year ago now.
Microsoft Publisher: zero-day macro policy bypass
It’s been a little while since we talked about Microsoft Publisher, so today’s publication of CVE-2024-38226 — a local security feature bypass for Office macro policy — gives us a chance to do that. The Preview Pane is not involved, and the description of exploit methodology in the FAQ is welcome, but somewhat unusual: an attacker must not only convince a user to download and open a malicious file, but the attacker must also be authenticated on the system itself, although the FAQ does not explain further.
Moving past those vulnerabilities which are known to be exploited or disclosed already, we see three critical RCE vulns: two in SharePoint, and one in the Windows NAT implementation.
SharePoint: two critical RCEs
Network-vector exploitation of SharePoint RCE CVE-2024-38018 requires that an attacker have Site Member permissions already, but since those aren’t exactly the crown jewels, attack complexity is low, and no user interaction is required, Microsoft very reasonably rates this as Critical on its own proprietary severity scale, and expects that exploitation is more likely.
The second SharePoint critical RCE patched this month is CVE-2024-43464, which describes a deserialization of untrusted data leading to code execution in the context of the SharePoint Server via specially-crafted API calls after uploading a malicious file; one mitigating factor is that the attacker must already have Site Owner permissions or better. This all sounds very similar to CVE-2024-30044, which Rapid7 wrote about back in May 2024.
Windows NAT: critical RCE
Rounding out this month’s critical RCE vulnerabilities is CVE-2024-38119, which describes a use after free flaw in the Windows NAT implementation. Attack vector is listed as adjacent, so an attacker would need an existing foothold on the same network as the target asset before winning a race condition, which bumps up the attack complexity to high. Even though this looks to be pre-auth RCE, Microsoft lists exploitation as less likely. For reasons unknown, Server 2012/2012 R2 does not receive a patch, although all newer supported versions of Windows do.
Exchange: nothing, still?
After a busy couple of months back in March and April 2024, it’s been all quiet on the Exchange front for quite some time, and this month extends that curiously lucky streak.
Microsoft lifecycle update
There are no significant changes to Microsoft product lifecycle during September 2024, although anyone responsible for Azure Database for MySQL - Single Server has until the sunset date of 2024-09-16 to migrate to a supported service to avoid involuntary forced-migration and server unavailability.
As Rapid7 noted last month, Visual Studio for Mac received its last ever patches on 2024-08-31. Also on 2024-08-31, a number of legacy Azure services reached retirement, including Azure Cache for Redis on Cloud Services (Classic).
October will see significant lifecycle changes for Windows 11: release end date for the 21H2 versions of Windows 11 Enterprise and Education, as well as release end date for 22H2 versions for other Windows 11 editions. Fans of legacy software will already know that Server 2012 and 2012 R2 move into year two of the cash-for-updates Extended Security Update program in October.
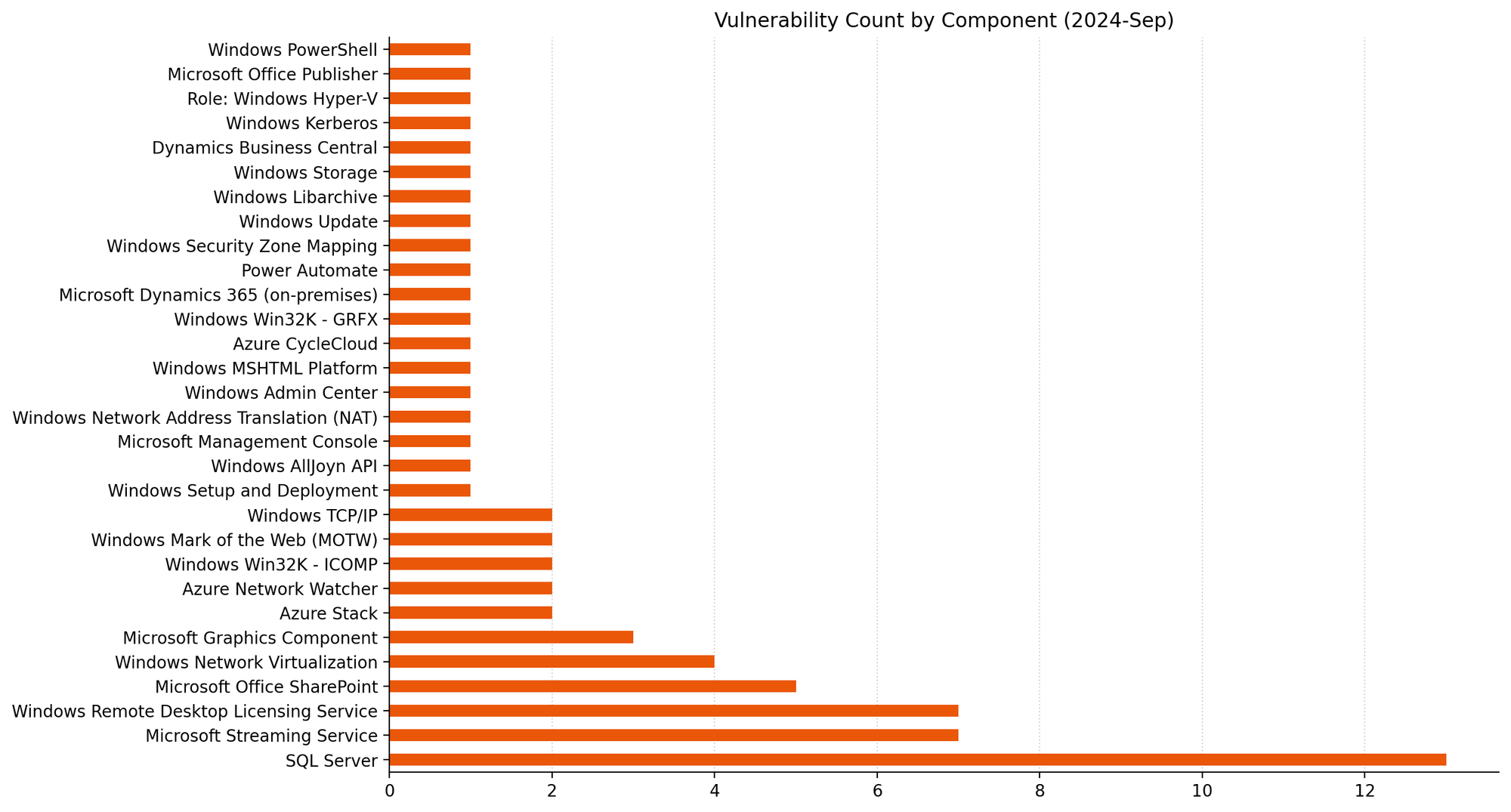
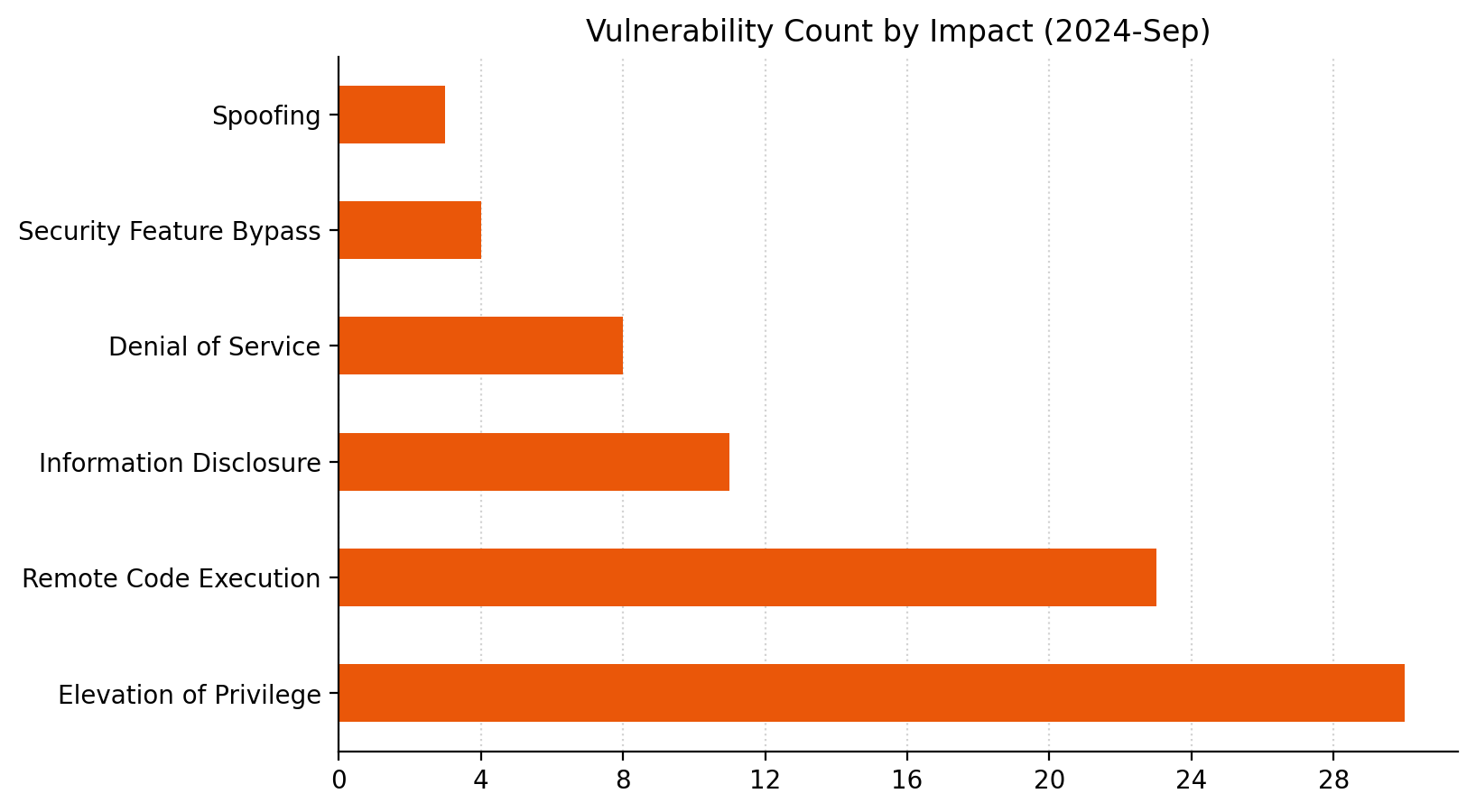
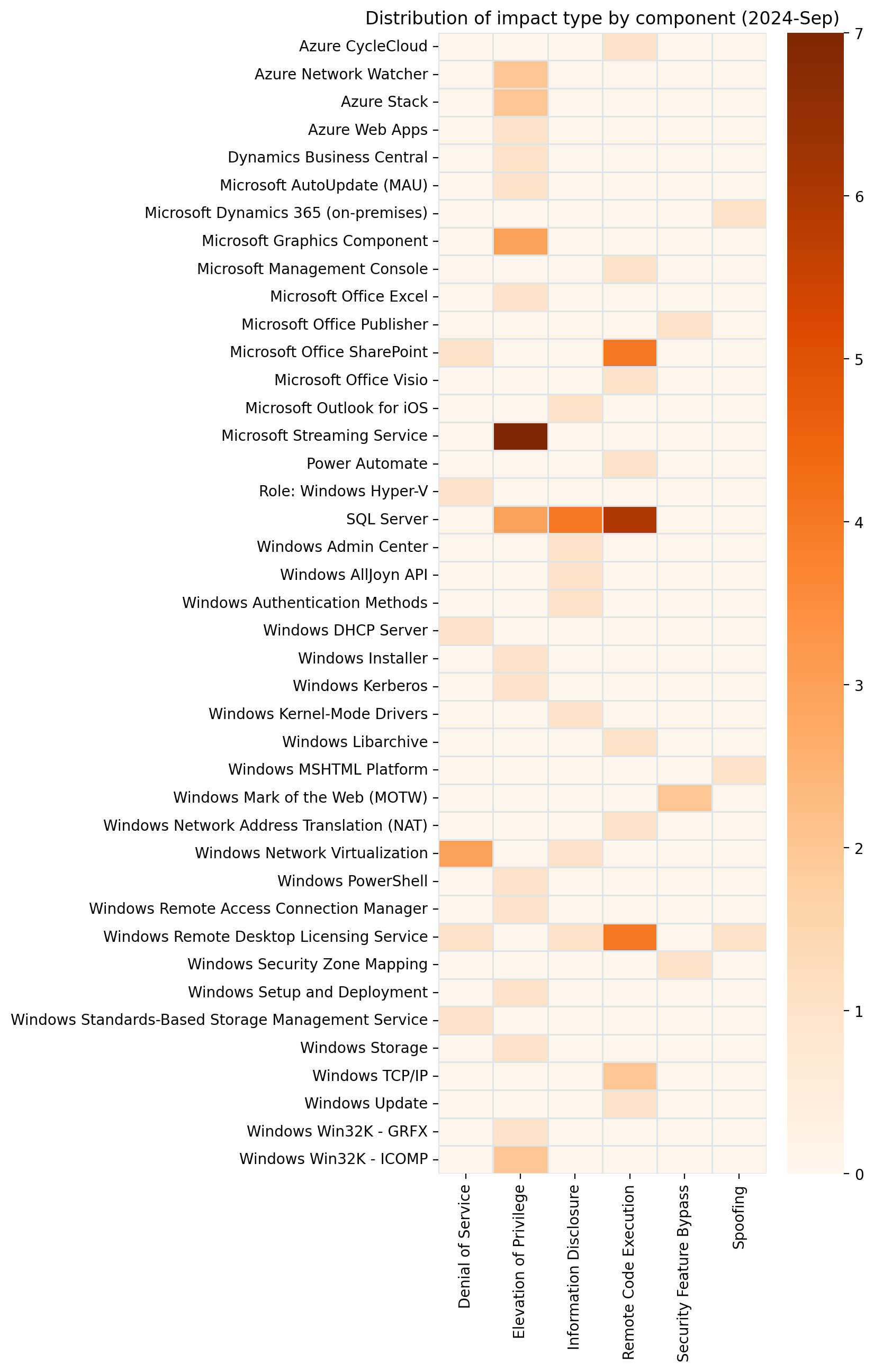
Summary charts
Summary tables
Azure vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38220 | Azure Stack Hub Elevation of Privilege Vulnerability | No | No | 9 |
| CVE-2024-43469 | Azure CycleCloud Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-38194 | Azure Web Apps Elevation of Privilege Vulnerability | No | No | 8.4 |
| CVE-2024-38216 | Azure Stack Hub Elevation of Privilege Vulnerability | No | No | 8.2 |
| CVE-2024-43470 | Azure Network Watcher VM Agent Elevation of Privilege Vulnerability | No | No | 7.3 |
| CVE-2024-38188 | Azure Network Watcher VM Agent Elevation of Privilege Vulnerability | No | No | 7.1 |
ESU vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-43475 | Microsoft Windows Admin Center Information Disclosure Vulnerability | No | No | 7.3 |
ESU Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-43455 | Windows Remote Desktop Licensing Service Spoofing Vulnerability | No | No | 8.8 |
| CVE-2024-38260 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43461 | Windows MSHTML Platform Spoofing Vulnerability | No | No | 8.8 |
| CVE-2024-38240 | Windows Remote Access Connection Manager Elevation of Privilege Vulnerability | No | No | 8.1 |
| CVE-2024-30073 | Windows Security Zone Mapping Security Feature Bypass Vulnerability | No | No | 7.8 |
| CVE-2024-38014 | Windows Installer Elevation of Privilege Vulnerability | Yes | No | 7.8 |
| CVE-2024-38249 | Windows Graphics Component Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38247 | Windows Graphics Component Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38245 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43467 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability | No | No | 7.5 |
| CVE-2024-38263 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability | No | No | 7.5 |
| CVE-2024-38236 | DHCP Server Service Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-38239 | Windows Kerberos Elevation of Privilege Vulnerability | No | No | 7.2 |
| CVE-2024-43454 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability | No | No | 7.1 |
| CVE-2024-38230 | Windows Standards-Based Storage Management Service Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-38258 | Windows Remote Desktop Licensing Service Information Disclosure Vulnerability | No | No | 6.5 |
| CVE-2024-38231 | Windows Remote Desktop Licensing Service Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-38234 | Windows Networking Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-43487 | Windows Mark of the Web Security Feature Bypass Vulnerability | No | No | 6.5 |
| CVE-2024-38256 | Windows Kernel-Mode Driver Information Disclosure Vulnerability | No | No | 5.5 |
| CVE-2024-38217 | Windows Mark of the Web Security Feature Bypass Vulnerability | Yes | Yes | 5.4 |
ESU Windows Microsoft Office vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38250 | Windows Graphics Component Elevation of Privilege Vulnerability | No | No | 7.8 |
Microsoft Dynamics vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38225 | Microsoft Dynamics 365 Business Central Elevation of Privilege Vulnerability | No | No | 8.8 |
| CVE-2024-43479 | Microsoft Power Automate Desktop Remote Code Execution Vulnerability | No | No | 8.5 |
| CVE-2024-43476 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability | No | No | 7.6 |
Microsoft Office vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38018 | Microsoft SharePoint Server Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43463 | Microsoft Office Visio Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-43465 | Microsoft Excel Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43492 | Microsoft AutoUpdate (MAU) Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38226 | Microsoft Publisher Security Feature Bypass Vulnerability | Yes | No | 7.3 |
| CVE-2024-43464 | Microsoft SharePoint Server Remote Code Execution Vulnerability | No | No | 7.2 |
| CVE-2024-38227 | Microsoft SharePoint Server Remote Code Execution Vulnerability | No | No | 7.2 |
| CVE-2024-38228 | Microsoft SharePoint Server Remote Code Execution Vulnerability | No | No | 7.2 |
| CVE-2024-43466 | Microsoft SharePoint Server Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-43482 | Microsoft Outlook for iOS Information Disclosure Vulnerability | No | No | 6.5 |
SQL Server vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-37338 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-37335 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-37340 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-37339 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-26186 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-26191 | Microsoft SQL Server Native Scoring Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-37965 | Microsoft SQL Server Elevation of Privilege Vulnerability | No | No | 8.8 |
| CVE-2024-37341 | Microsoft SQL Server Elevation of Privilege Vulnerability | No | No | 8.8 |
| CVE-2024-37980 | Microsoft SQL Server Elevation of Privilege Vulnerability | No | No | 8.8 |
| CVE-2024-43474 | Microsoft SQL Server Information Disclosure Vulnerability | No | No | 7.6 |
| CVE-2024-37966 | Microsoft SQL Server Native Scoring Information Disclosure Vulnerability | No | No | 7.1 |
| CVE-2024-37337 | Microsoft SQL Server Native Scoring Information Disclosure Vulnerability | No | No | 7.1 |
| CVE-2024-37342 | Microsoft SQL Server Native Scoring Information Disclosure Vulnerability | No | No | 7.1 |
Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-43491 | Microsoft Windows Update Remote Code Execution Vulnerability | Yes | No | 9.8 |
| CVE-2024-38259 | Microsoft Management Console Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-21416 | Windows TCP/IP Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-38045 | Windows TCP/IP Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-38252 | Windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38253 | Windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43457 | Windows Setup and Deployment Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38046 | PowerShell Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38237 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38241 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38242 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38238 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38243 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38244 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43458 | Windows Networking Information Disclosure Vulnerability | No | No | 7.7 |
| CVE-2024-38232 | Windows Networking Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-38233 | Windows Networking Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-38119 | Windows Network Address Translation (NAT) Remote Code Execution Vulnerability | No | No | 7.5 |
| CVE-2024-38257 | Microsoft AllJoyn API Information Disclosure Vulnerability | No | No | 7.5 |
| CVE-2024-43495 | Windows libarchive Remote Code Execution Vulnerability | No | No | 7.3 |
| CVE-2024-38248 | Windows Storage Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-38246 | Win32k Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-38235 | Windows Hyper-V Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-38254 | Windows Authentication Information Disclosure Vulnerability | No | No | 5.5 |
NEVER MISS AN EMERGING THREAT
Be the first to learn about the latest vulnerabilities and cybersecurity news.
Subscribe Now